- Airtable Community
- Discussions
- Ask A Question
- Other questions
- Field-level Encryption: Does Anyone Care?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark
- Subscribe
- Mute
- Printer Friendly Page
Field-level Encryption: Does Anyone Care?
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Dec 22, 2020 07:31 AM
We do a lot of difficult things for clients - from complex integrations to crazy mapping and data visualizations. But a recent project required field-level encryption in the new Google Tables product as well as Airtable.
Encryption Scenario:
-
User fills out a form and reveals confidential information in one or more form fields targeted for encryption.
-
The user also enters a “passkey” - think pin-code like “2998” or a password like “good1ucktryingt0geu$$this”.
-
The form is submitted and an action script immediately transforms the entry in many ways.
-
The target encrypted fields are combined into a collection of strings and encrypted using a 256-bit AES algorithm resulting in a single cypher key.
-
All targeted encryption fields are set to null values.
-
The cypher created as a result of step #4 is then transformed into a GUID and placed into a designated field in the record
With this process, which occurs in about 800ms, the record entered by the user is now obscured; the sensitive data is stored in the cypher key which looks like any GUID (i.e., 25bdd861-1aa1-4626-832f-f7cabf4b57ae).
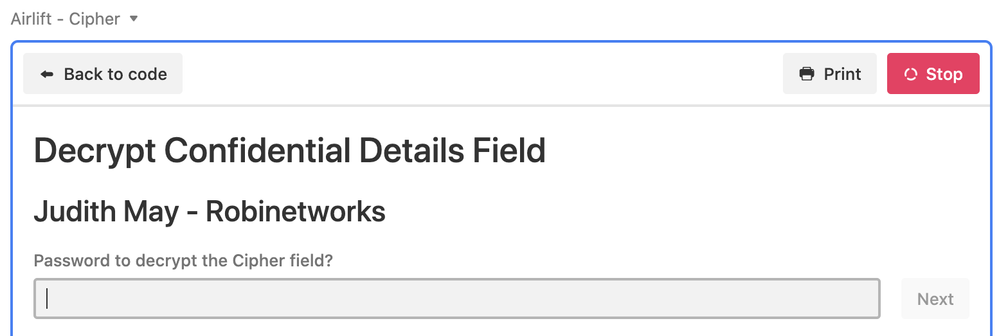
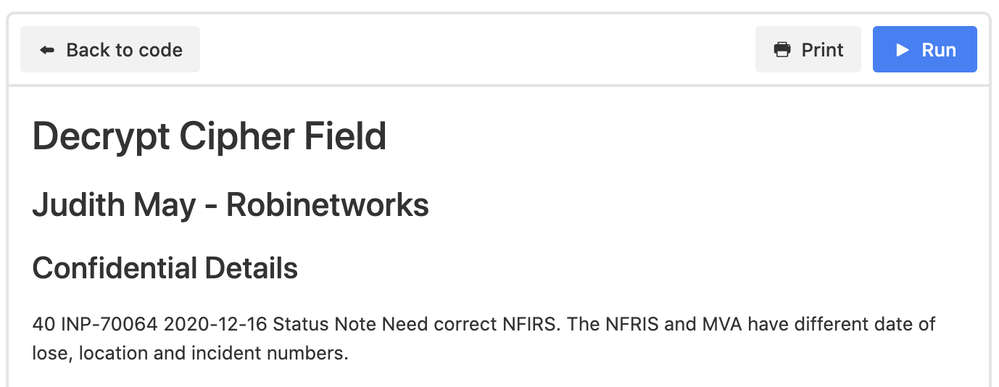
Now imagine a Script Block (or a custom app, or an API process) that can access and display the sensitive information. It is able to prompt for the pass key -
Successful entry of the passkey displays the designated sensitive information.
Alternatively, the passkey is sustained in a session allowing the user to browse sensitive data as demonstrated in this video.
Does anyone care about scenarios and encryption like this?
sidebar - it’s important to note that the record creation action stores a version of the unencrypted data, thus making it possible for anyone with read access to see historical versions. As such, the true layout of this process in production requires an additional abstraction from the consumable data records. I didn’t want to complexify the scenario, but it’s also an important design choice to make it impossible to expose sensitive data that arrives via Airtable or Google Tables forms.
- Mark as New
- Bookmark
- Subscribe
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sep 27, 2023 06:32 AM
Hi Bill,
I found this old post of yours, and I am wondering if things have improved for Airtable encryption/data security features since you wrote it.
I'm looking for a good way to store encrypted info in dedicated fields in my Airtable, alongside other non-encrypted and non-sensitive fields, then allow authorised users to view the records, including decrypted data fields, through a console app of some kind, so they can perform various tasks that require this data.
So far, I can encrypt the data in Make using AES256 and can store the encrypted strings to Airtable.
I was assuming I would need to create an external console app, and use webhook from that app to trigger Make to decrypt and populate data to make it visible in that app, but I thought I should check if Airtable can offer anything along these lines, maybe via Interfaces or Extensions, that might make it more possible to do this kind of thing inside Airtable?
Any insights will be much appreciated.