Hi all,
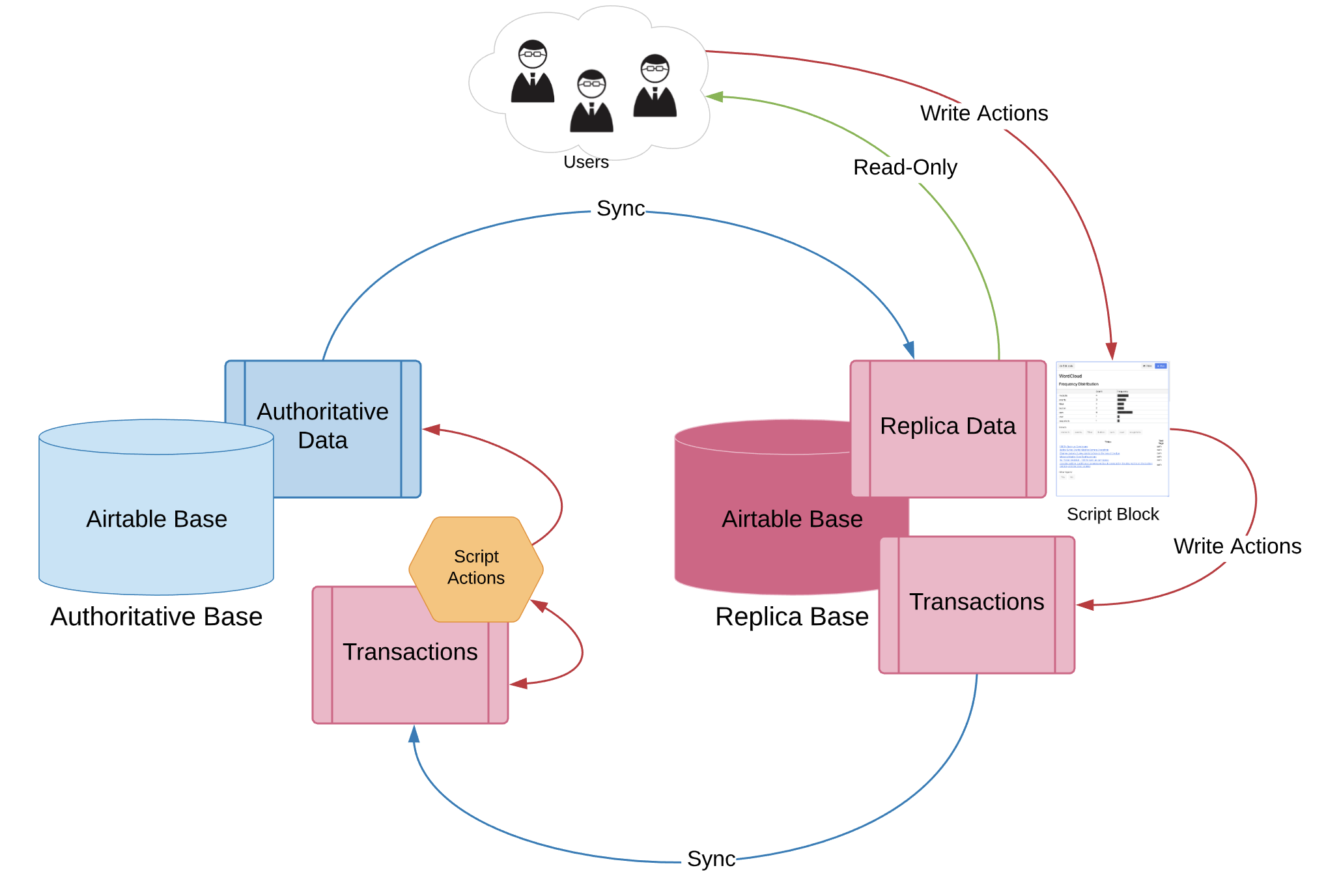
Wondering if anybody knows of a workaround that allows one to set user permissions to only allow changes (edit / create / delete record) through code (scripting block in my case).
This would come in very handy when you don’t want base users to mess with the content or structure of your base, but would still allow them to add/edit/delete records through the scripting block, therefore enforcing your desired business rules.
@Airtable Team, any suggestions? should we expect this feature in the near future?
Thank you,